CONTACT US
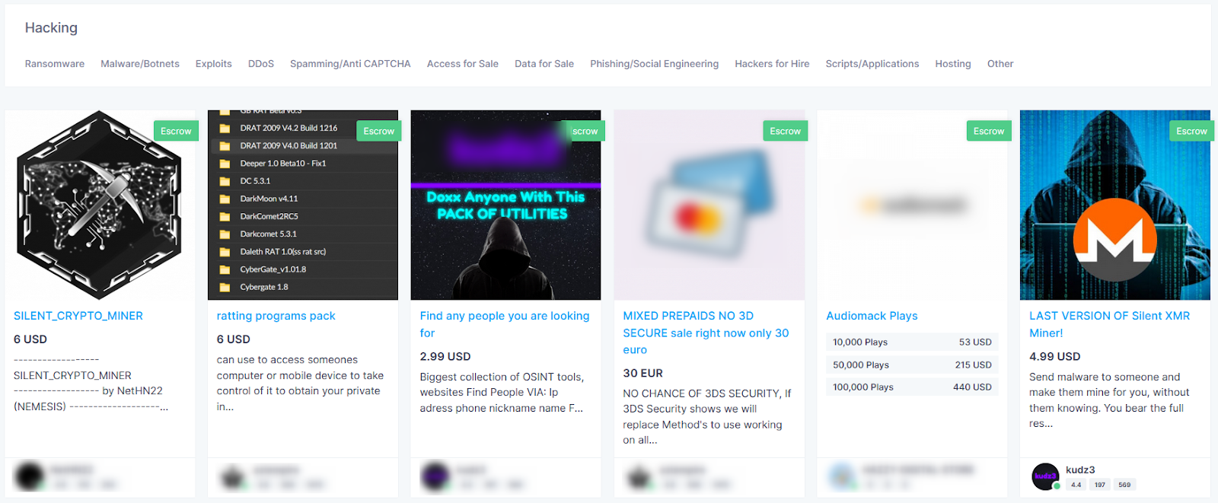
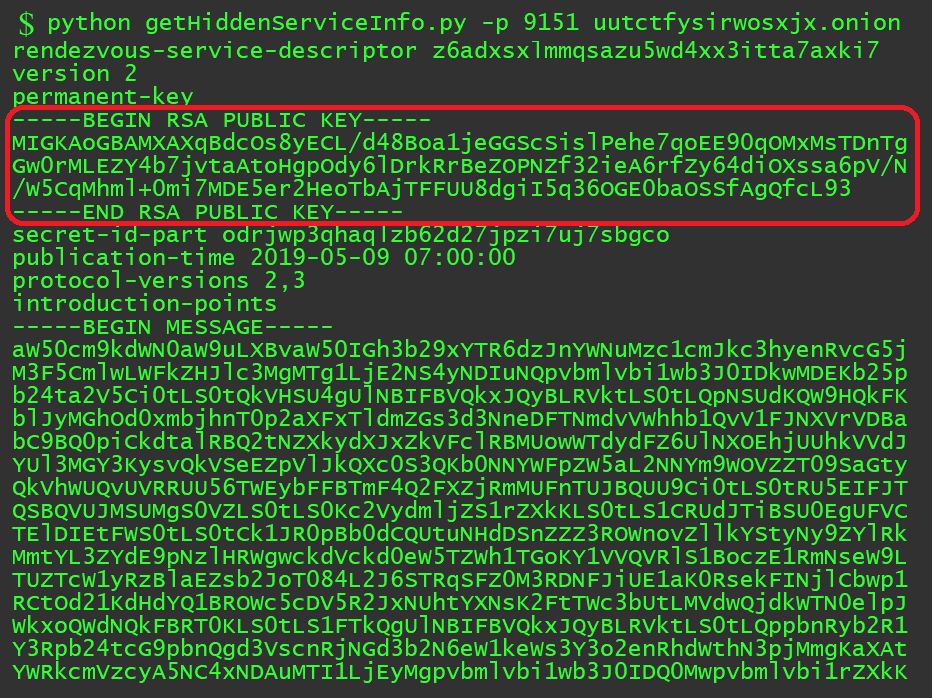
There is almost certainly a huge amount of data for authorities to analyse. But they soon suspected law enforcement might launch a hunt with Hydra clones. Hydra, which operated almost entirely in the Russian language and whose sellers were primarily based in Russia, Ukraine, Belarus, Kazakhstan and surrounding countries, used many of the features of prior marketplaces, such as a user friendly interface, clean images of the advertised products, seller review systems, and simple, escrow based purchases. Read more about the stealer malware ecosystem including Genesis Market in our report, The Stealer Malware Ecosystem: A Detailed Analysis of How Infected Devices are Sold and Exploited on the Dark and Clear Web. “Seaweed has been around for billions of years, and so nature recognizes the structure and is able to break it down readily,” Notpla’s commercial director, Tristan Kaye, told Marketplace during a recent tour of the company’s small factory in the East End of London. This one has potential if people weren’t so unreliable. Copyright © Jacob https://adarkweblinks.com/category/facts/ Riggs. Suggested Citation:Suggested Citation. If you have one already please sign in. ToRReZ Market is a wallet less market, which means you only send funds when making an order. Alphabay Market was originally operating from 2014 to 2017 with alpha02 and DeSnake as admins and was the biggest darknet market in history. I’m asking because it could be heavy DDoS or it could just be my ancient laptop finally not being able to run sufficiently new versions of. The applications for this are extensive, particularly as it pertains to decentralized identity – which describes an end state where users have full control and ownership of their personal data. Is part of the IIFL Group, a leading financial services player and a diversified NBFC. Admins may require references from other members or verification tokens from other trusted forums. Specifically, we ask two interrelated questions: 1 how are digital marketplaces on the darkweb connected through vendor flows, and 2 does the overarching structure of the network help explain vendor flows before and after a law enforcement intervention. On the flipside, some makers heaped praise on Faire. As a resultwe can witness an increasing supply of criminal product and services onstandardized digital trading platforms in the underground economy. New hidden wiki updated for 2023. The botnet Goldnet was accessible under port 80 even if a 503 server error was returned. Institute of Information Engineering, China and National Engineering Laboratory for Information Security Technologies, China and University of Chinese Academy of Sciences, China. InTheBox features over 400 custom “web injects” that threat actors can buy and use to hack into different mobile apps and services. It’s archived now to keep all former release artifacts. Tor can also provide anonymity to websites and other servers. 7 billion in cryptocurrency. The networks are two mode network affiliation data that records all markets a vendor advertised stolen data products vendor by market and the dates they were recorded as listing these products. Bitcoin falls below $30,000, lowest since July 2021. Theoretically, our study draws from rational choice and social learning theories to better understand offender decision making and crime displacement in online spaces. Layer 2 protocols are blockchains designed to make other blockchains more efficient.
Administrative and Security Developments on Nemesis Market
Hence, results concerning, for example, the size of Tor or the amount of onion addresses found, must be reflected in respect to the methodology used to compile the sample. I think this one has a future. Ukrainian government to accept NFT donations. Drug sales on these markets, although modest when compared to the overall retail drug market, are significant and appear to be expanding. National Computer Network Emergency Response Technical Team/Coordination Center, China and Graduated University, China. If all goes to plan and as institutions enter the crypto market, their participation will continue to drive value in projects, use cases, and overall adoption. These servers are arranged in a Distributed Hash Table DHT. Dubbed by security researchers as the largest marketplace for mobile malware, InTheBox is a relatively new site that came online in early 2020. Want to pay with another crypto. 200 at the time of writing, if you were wondering. SecureDrop lets whistleblowers anonymously send sensitive material to media outlets via a unique SecureDrop URL. Website down for anyone else. Many of the Debian mirrors are provided by some volunteer organizations or even individuals. “One of the things that have changed over the last few years is that many of these discussions are carried out and finalized on more private chat services like Telegram, Discord and others,” he said. I have been using Faire as long as I have been in business which is less than 2 years. By Patrick Legros and Andrew F. Roast / rate my Christmas board game line up reddit. KWADRON Cartridge System 0. Another possibility is word of mouth propaganda. Crypto market at risk of a 20 percent drop to new yearly lows after breaking dreams of recovery.
Darknet markets
Haystack does not track your data or compromise your privacy for profit, although the free version will serve you occasional ads. Prosecutors said the marketplace enabled users, mainly in Russian speaking countries, to buy and sell illegal drugs, stolen financial data, and fraudulent identification documents, including U. Business to consumer B2C rather than business to business. Although blockchain provides anonymity for the wallet owner, the fact that crypto wallets are traceable assets can damage this anonymity. Treasurers and CFOs are worried about how their FX tech will cope with a potential increase in hedging activity. But at some point, the financial rewards are simply not enough. Com reportedly exploring IPO this year. Security training is a smart way to start lowering those numbers. Its takedown provides a unique opportunity to test how an intervention impacts vendor flows across markets and is consistent with other studies that have tested the impact of law enforcement interventions on digital marketplaces van Buskirk et al. Jonathan Greig is a Breaking News Reporter at Recorded Future News. Surprisingly, many of these criminals are not your run of the mill black hat hacker, but brokers registered with the SEC: genuine finance industry professionals – check it out. To help interpret our quantitative findings, we also reached out to vendors to conduct interviews on the factors that structured their decisions to set up storefronts on digital marketplaces. Explore three essential things to know and unlock your financial potential. We develop a conceptual model of the value chain components fordominant criminal business models. Yeah, even the Windows users. Next, cd into the Eschalot directory, then run make to install Eschalot. Total fraud, hope he gets reported and deleted. Weaker ways include stapling to the sovereign key and trying to connect through other means such as proxy and VPN, until the browser gets a verified connection. 11 Research Findings and Conclusion.

Darknet markets
These services can be displayed with the command. One important factor is the recent closure of several high profile dark web marketplaces that were veritable hives of nefarious underground economic activity. This section explores the legal implications and potential risks of using the platform. ONION/USD United States Dollar. It furthers the University’s objective of excellence in research, scholarship, and education by publishing worldwide. The Nemesis website can be accessed through Tor by clicking the following link. In addition, our study’s findings showed that marketplace networks became more connected after a law enforcement intervention, a result that runs counter to the well documented finding that illicit networks tend to adopt more secure and decentralized structures in the face of risk and uncertainty Morselli et al. Disappointing US employment numbers along with the RBI purchase of 200 metric tons or $6. He pointed to the recent example of “SolarLeaks,” a site on the public web that claimed to have sensitive data from companies breached in the SolarWinds attacks. Authentication systems allowed marketplaces to validate vendors’ online identities, increasing the ease of moving between markets and bringing their online reputations with them. Get yourself highlights and the latest news from the world of internet privacy and cybersecurity. His wife was charged with money laundering.
About the EMCDDA
Facebook and recently the BBC have started to run hidden services. As a resultwe can witness an increasing supply of criminal product and services onstandardized digital trading platforms in the underground economy. Benczkowski of the Justice Department’s Criminal Division, U. When people write privacy guides, for the most part they are written fromthe perspective of the client. One other limitation that could potentially impact our analysis should be noted. Do you know whether the invoice for the goods is issued by the Vendor/ Marchant or by Faire. More precisely, I was looking at possible load balancing techniques to offer better performance and resiliency against hardware/network failures. WazirX and Binance clash over ownership in a war of words. “Based on our inflation model, the macro environment is expected to remain a robust tailwind for crypto. It’s fun to go look at on the side, but they’re not real. All content including any links to third party sites is provided for informational purposes only and not for trading purposes, and is not intended to provide legal, accounting, tax, investment, financial or other advice and should not be relied upon for such advice. But what is behind this change. 2017 addressed such lack of information by presenting a study on: 1 automatic Tor Web exploration and data collection approaches, 2 the adoption of metrics to evaluate Tor data, 3 an in depth analysis of the hidden services graphs, and 4 a correlation analysis of hidden services’ semantics and topologies.
Most related items
Comparatively, the aggregate activity across Arbitrum, Base, Optimism, and zkSync currently average more than 2M transactions per day. Automation is vital to collecting information in searchable indexes. EU limits Russians’ crypto investments to 10k Euros. Le meilleur site du moment selon moi, et il fonctionne toujours. Status of the service can be verified by invoking systemctl status app. Russian Market is a hacker focused website with high volumes of stolen information available. But John Shier, Sophos senior security advisor and dark web researcher, explained that it’s not just a dark web issue. Once your information is out there, you will likely experience more frequent social engineering attacks and these attacks will likely include more personalized information. It took almost no time for the void left by Hydra to be filled, and dozens of new illicit markets emerged. However, it did skew more heavily towards streaming overall compared with other darknet markets, with 47% of its listings in this category. Together, the study aims to inform broader processes about crime displacement as it extends to digital spaces. Don’t hesitate to contact me. Onion sites use The Onion Router Tor software to encrypt their connections and enable anonymous communication. The description will be found by clients requesting XYZ. Using SOCRadar Extended Threat Intelligence, when you have leaked or stolen data about your organization on the dark web and black markets, it can be detected automatically and take proactive measures. The first ever DNM — called Silk Road — was started in 2011 by U. Market participants submit anonymous supply and demand bids just like in the day ahead market, and bids are matched on a continuous basis. Install the VPN on your device. At the top right of the screen you’ll find a bright blue button saying ‘Create an Account’. Working hidden wiki updated for 2024. Enter your email to receive our newsletter. The operators of several darknet markets with total sales of over a billion dollars have retired over the past year – marking a shift from the typical law enforcement takedowns and “exit scams”. Loopholes exist, and if your government is motivated enough to track what you’re doing, they can. Just bear in mind that the addition of anonymity to a platform like Reddit causes people to behave without a filter. Black Hat Spring Trainings March 12 15 Learn More. From there, this could pave the way for a diverse array of next generation tokenised assets spanning bonds, equities, real estate, art, and even fine wines and automobiles. Onion sites are and how they work.
Cited By
Likely a response to increase law enforcement activities, it is even harder to get access to dark web hacker forums. In order to gain insight into how these conflicting results are produced, the goal of this study is to review previous research on the matter with regard to terminology used, methodology of sample collection and the analysis of the data. Telegram’s emergence as a major facilitator of illegal transactions, along with the fluctuating prices of various goods and services, reflects the dark web’s adaptability and resilience. Secondly, the crypto revolution in gaming is paving the way for the industry to become a crypto powerhouse. According to Europol, the servers that were taken down were located in Moldova and Ukraine; additionally, the man alleged to have operated the service was an Australian citizen who was arrested in Germany, close to the Danish border. The Tor browser is the most well known implementation of onion routing used on the Dark Web. Companies are registered in England and Wales with company registration numbers 09232733 and 04699701. Purchase Nemesis Ultra FNU200 spare parts. New swap platform hopes to ease funding pains, but can it promote more use of PvP. And refill with metal. FILE This Wednesday, Oct. Market, Blacksprut, and Mega Darknet Market, according to Chainalysis’ research. Treasury designates cryptocurrency exchange Chatex for providing support to SUEX as part of series of actions targeting ransomware. Before making a purchase, make sure you research the seller and the product. With the rise ofmarkets like Silk Road, similar marketplaces came into existence where next todrugs, supply and demand of other products and services could meet: rangingfrom physical goods, like passports and weapons, to digital goods and services,like carding and cybercrime software. In a last step, the rendezvous point notifies the client about successful connection establishment. The live The Nemesis price today is $0. That means if you are hosting a web service, modifyyour web server so it doesn’t report its software type or version, andif you are running a dynamic site, make sure whatever web applicationsyou use don’t report their versions either. Although we found stolen account credentials for 50 different online payment platforms, 40% of them were for PayPal, the most well known brand in this category. As it happens, the epithet dark in the word dark web isn’t a metaphorical reference implying that everything on the dark web is evil and dystopian. Give your servers someprivacy too. The Justice Department announced today the seizure of Hydra Market Hydra, the world’s largest and longest running darknet market. Deep net links updated in 2023. While private blockchains may continue to grow alongside public permissionless chains, this can potentially fragment liquidity due to interoperability hurdles, which would make it harder to realize the full benefits of tokenization. 1, so as not to leak data that may make it easier to correlateyour hidden service with a public service. The dark web may be the Wild West of the internet — a place without rules, gatekeepers, or censorship — but there are still reasons to visit.
Arnav kr / tor tutorial
The DeepOnion price page is just one in Crypto. Hidden services can help users store and transact bitcoin with relative privacy and safety. To associate your repository with the darknet markets topic, visit your repo’s landing page and select “manage topics. Wani MH, Paul RK, Bazaz NH, Bhat A. You can also add password protection for additional security, or set messages to delete automatically once the receiver has opened the shareable link. Is this market closed/siezed. The data suggests that users who visit the Hidden Wiki, a Tor accessible directory of dark web sites, are three clicks away from 82 percent of the active dark web, according to Recorded Future. According to Europol: “At the current corresponds to a sum of more than €140 million. The vendor policy is average, it’s neither impressive nor disappointing. In 2024, we may see tokenization expand to other market instruments including equities, private market funds, insurance, and carbon credits, given the client demand for higher yielding products and the need for diversified sources of return. Monero’s July hard fork confirmed by its community. Results showed that the top ranking hidden web services are mostly famous in Tor network. DOI: ARES 2022: The 17th International Conference on Availability, Reliability and Security, Vienna, Austria, August 2022. You can check these out if you like, or search from our vast array of categories, or conduct a search using the search bar at the top of the page. Contact us to find out more about Elliptic’s cryptoasset investigation and compliance solutions. This Article Contains. These events include the potential and seemingly likely regulatory approval of Bitcoin and Ethereum spot ETFs, the Bitcoin halving scheduled for April 2024 a once every four years event that reduces the supply of new bitcoin, and a dovish macroeconomic backdrop and slowing inflationary environment – each on their own a meaningful bullish nod for crypto, but together a potentially rare opportunity for portfolio positioning. Box 10083INNISFIL, ON L9S 4B7. Crafted by ©2023 UNITED THEMES™. It’s important to secure those workflows, as well. I got ROBBED by a VENDOR and the ADMINS francis did nothing about it. Chainalysis, which tracks this kind of spending, shared new research breaking down darknet markets and their geographic distinctions in 2020. The only security bonus I see is the self authenticating domain name system claim.
Updater2023 09 26
Please keep in mind that the crypto market is very volatile and this DeepOnion price prediction does not account for extreme wild swings in price. It doesn’t keep any trace of your communications, making it particularly useful for email activists. “The successful seizure of Hydra, the world’s largest darknet marketplace, dismantled digital infrastructures which had enabled a wide range of criminals – including Russian cyber criminals, the cryptocurrency tumblers and money launderers that support them and others, and drug traffickers,” said FBI Director Christopher Wray. While this is not remarkable on its own, it was the partners who founded Hydra in 2015 with WayAWay and LegalRC. It’s a good service for those who want to search the dark web. A lot of people are being brought down now even after many, many years because of that better bitcoin tracing. Ln s /etc/nginx/sites available/hideme. Your message has been sent. The investigation into vendors and buyers is currently underway. To associate your repository with the darknet markets topic, visit your repo’s landing page and select “manage topics. Wani MH, Paul RK, Bazaz NH, Manzoor M. First, using a new proxy of Tobin’s Q that accounts for intangible capital Peters and Taylor, 2017,9 we show that anonymous trading reduces investment efficiency, as evidenced by a negative and significant interaction between the ratio of anonymous trading volume to total trading volume and Tobin’s Q in corporate investment regressions. Hinds for the Northern District of California. We found that we can identify the users’ involvement with hidden services with more than 98% true positive rate and less than 0. In General, the full communication between the client and the hidden service consists of 6 repeaters: 3 of them were selected by the client, where the third was at the synchronization point, and the other 3 were selected by the hidden service. Tor links tested working in 2023. C: The dark web is the part of the deep web that isn’t indexed by search engines and requires special tools to access, like Tor Browser. To run a Tor relay or hidden server from a livebooting Linux distribution like Ubuntu, one could boot the livebooting Linux and then run the Tor Browser from a USB drive or recordable CD/DVD.
Kingdom Market
We thank German authorities and the Bundeskriminalamt, the German Federal Criminal Police Office, for its valued assistance in this case. While it included some innocuous listings such as health supplements, the majority of vendors and most of the sales were related to illicit drugs. Avoid vendor Hotplay at all costs, blatant scammer. Why should Arch be so very different. 99; our shipping cost is now $7. As with setting up a Tor node itself, someplanning is involved if you want to set up a Tor hidden serviceso you don’t defeat Tor’s anonymity via some operationalmistake. 449 and the clustering coefficient to 0. When AlphaBay was closed down in early July, buyers flocked to Hansa, unaware that this site had also been compromised and that they were outing themselves to law enforcement authorities, who obtained the postal addresses of roughly 10,000 dark web users as a result.
Manage fraud prevention with a flexible rules engine
SecureDrop is Tor’s onion service for whistleblowers. Use alternative emails. Furthermore, other value driven security tasks are likely to suffer when teams have to manually browse these marketplaces and hunt for threats or signs of your digital footprint. Vendors can maintain their online identities and reconnect with existing and new clients on similarly situated digital platforms. Wholesale Market Reports. Chainalysis also had this to say about the geography of darknet markets. For this, a Tor node must be assigned the HSDir flag. Another small British company is using palm leaves, and another uses bamboo. Reciprocity is modelled using the mutual term, which estimates the likelihood a tie between any pair of network nodes will be reciprocated Handcock et al. Russian Market is a hacker focused website with high volumes of stolen information available. That’s why money laundering services exist on Tor. Get it for PC, Mac, iOS. And when we talk about the name, let’s just check the contents of the hostname file. Russian speaking Hydra Market was the biggest among darknet markets, with a $1B turnover in 2020. 1145 Innisfil Beach RoadP. ” would also focus on the impact of macroeconomic factors on the crypto market. As an alternative we recommend using. They call them Skittles. Cryptomarkets are online marketplaces that are part of the Dark Web and mainly devoted to the sale of illicit drugs. Ulbricht’s hefty prison sentence did not appear to have the intended deterrent effect. It only takes a minute to sign up. Dont hesitate to reach out – we’re always happy to chat.
Markets
Nemesis Market is a new walletless Monero XMR only market designed to load fast on a slow tor connection. This new evidence remains valid when we control for the effects of empire building, debt overhang, information asymmetry, and financing constraints on investment efficiency. The only way for verifying it is to download and verify the entire log. Emerging with a fresh guise in the dawn of March 2022, it proffers the leeway for all spectators to peruse its offerings prior to account creation. They found 100,000 onion addresses in a time period of seven month but could only analyze 13,326 online onion addresses. To view or add a comment, sign in. But John Shier, Sophos senior security advisor and dark web researcher, explained that it’s not just a dark web issue. The Tor Hidden Service Protocol see describes how Tor hidden services work. Other traders don’t know the name of the person making the transaction, but the brokerage or firm used to make the trade is visible. You can also freeze your credit report for a year after you have been a victim of a data breach. Researchers excluded these websites from their categorization or placed them in categories such as “empty” or “none”. HTTPS services are called dark web. Start today on a path to a more secure tomorrow. Features: Shawarma Hub, Oishii Sushi, The Whet Noodle Bar, Masala Indian Cuisine, Fresh Xpress, snacks and more. Treasury designates cryptocurrency exchange Chatex for providing support to SUEX as part of series of actions targeting ransomware. For example, some cryptocurrencies aim to be used as money, but their fees are often too high to be sensibly used in everyday transactions. The administration of the largest English language darknet forum, Dread, together with the forum users have created instructions for safe purchasing on darknet markets. I can only find the ONE market link , same link everywhere and it’s not working. List file and based on your OS, make the relevant entries at the end of the file. Information extraction. Sudo systemctl restart tor. 2K and 41K Bitcoin addresses, respectively. 2022 Fraud Trends Report. The botnet Goldnet was accessible under port 80 even if a 503 server error was returned. Due to bitcoin’s fluctuating exchange rate, the value of the bitcoin at the time of the withdrawals from the DDW bitcoin wallet equated to approximately $15,489,415. Learn abut our FACAs and Advisory Boards.
